How to Reverse a Purchase Order Receipt in SYSPRO
SYSPRO makes it easy to reverse a mistake.
Perhaps you entered a wrong price, received the wrong item, or maybe received one too many quantities of an item on your purchase order. It is easy to get familiar with the process of receiving items. However, what do you do when you make a mistake and need to reverse a SYSPRO PO receipt that was not quite right? As long as a received item has not yet been sold, adjusted, or transferred, then SYSPRO makes it easy to reverse a mistake. We will explain the process of reversing a PO receipt in this article.

For our test example, we have received a quantity of 5 for our stock code “A100” that we would like to reverse. To do so, we need to go to the Purchase Order Receipts program in SYSPRO. This program can be found in SYSPRO’s program list at Purchase Orders Purchase Order Processing Purchase Order Receipts.
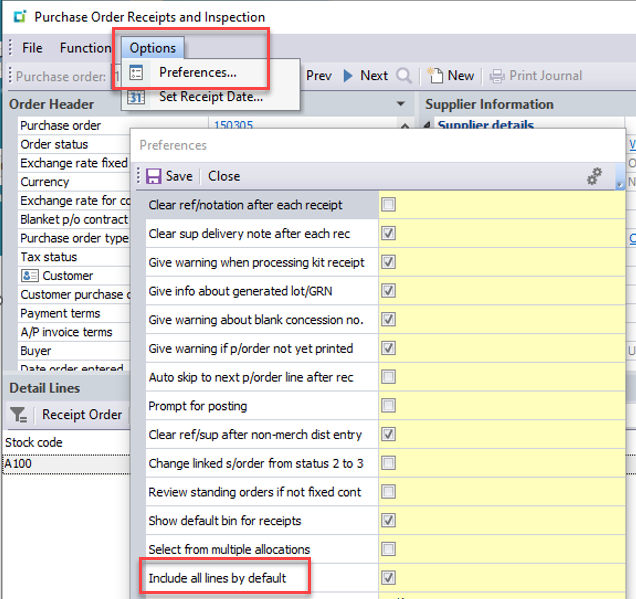
In the Purchase Order Receipts program, type in or browse to find the original purchase order number that your stock code was received on. If you received your PO line in full, you may notice that there are no lines showing on your PO to be received and you can’t find the original PO line for your stock code. This is because the program hides completed lines by default. To see your completed line, click on the “Options” tab at the top of the screen and select “Preferences…”. On the preferences screen, find and check the option that says, “Include all lines by default”. Click “Save” and the program will now show any completed lines on the selected purchase order.
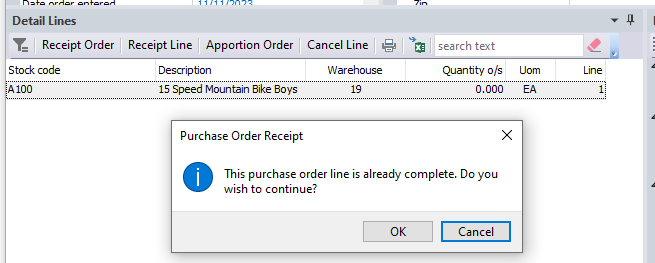
Now, find and select the purchase order line that you are wanting to reverse. Click the “Receipt Line” button or you can also double-click on the specific line to be reversed. If your line was completed by the original receipt, you will see a warning message. Click “OK”.
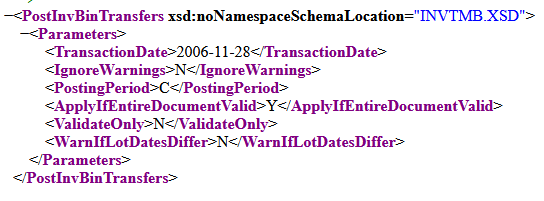
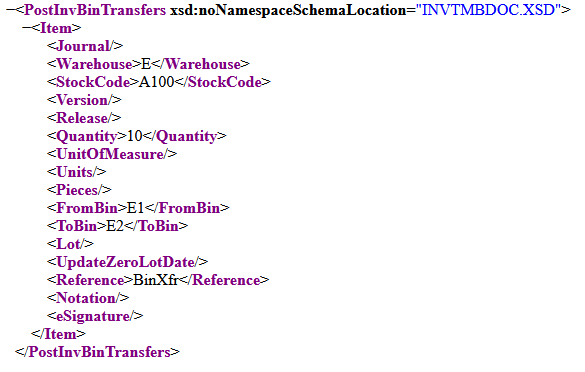
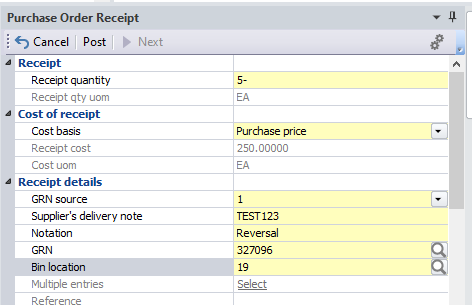
The “Purchase Order Receipt” pane will refresh with the details about the PO line. You will now have to do the following:
- Enter a negative “Receipt quantity”. In our case, we want to reverse the full quantity of 5 so we enter a value of “-5”.
- Select the original cost basis.
- Enter any supplier’s delivery note if applicable.
- Optionally, you can enter a notation to explain why the transaction is being reversed.
- Enter the GRN number that was created when the item was originally received.
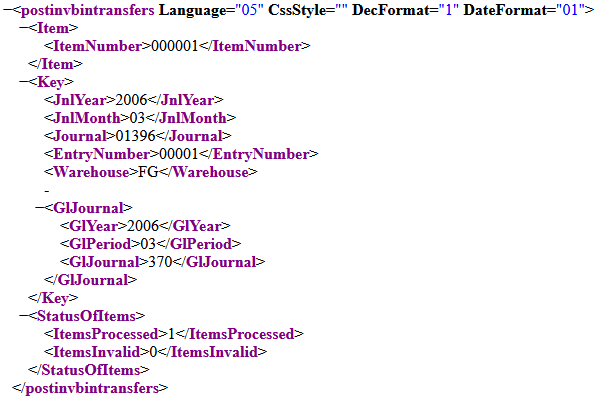
Click “Post” and the purchase order line receipt has now been reversed. You can verify the reversal by going to SYSPRO’s Inventory Query and check the “Movements” details for the stock code.
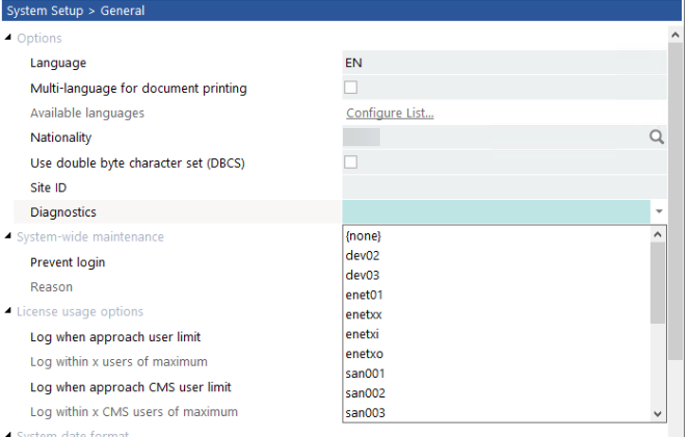
Adjusting preferences in SYSPRO ERP is easy.
Reversing a Purchase Order (PO) Receipt in SYSPRO ERP is a straightforward process that allows users to correct mistakes such as wrong prices, incorrect items received, or excess quantities. By accessing the Purchase Order Receipts program in SYSPRO, users can easily locate and select the original PO line to be reversed. Adjusting preferences to include all lines by default enables visibility of completed lines for reversal. Upon selecting the desired line, entering a negative receipt quantity, original cost basis, supplier’s delivery note if applicable, and a notation for explanation, if needed, facilitates the reversal process. Finally, posting the transaction confirms the reversal, which can be verified in SYSPRO’s Inventory Query. This systematic approach ensures accuracy and efficiency in managing PO receipts within the SYSPRO ERP system.
Are you seeking expert guidance and support for your SYSPRO ERP administration, implementation, and ongoing maintenance?
Look no further than EstesGroup consultants! Our team is dedicated to assisting you every step of the way, whether you’re setting up your system for the first time or looking to optimize its performance. With years of experience in SYSPRO ERP, we specialize in building, maintaining, and upgrading full-suite technology and cloud services tailored to your specific needs. From initial setup to continuous support and upgrades, we’re here to ensure your SYSPRO system runs smoothly and efficiently. Don’t hesitate to reach out to us today for personalized assistance and take your SYSPRO ERP experience to the next level!