Freight Forward to the Future: P21 Web UI Migration Options
Transitioning to the P21 Web UI Version
Keeping your Prophet 21 ERP system up to date poses numerous challenges, especially when dealing with upgrades. The testing, retesting, troubleshooting, and remediation processes can be time-consuming and demanding. Transitioning to the P21 Web UI introduces even greater challenges, with larger changes, increased risks, and heightened frustrations for end users. Consequently, the adoption of the P21 Web UI has been progressing slowly, akin to molasses in January, as they say in Canada.

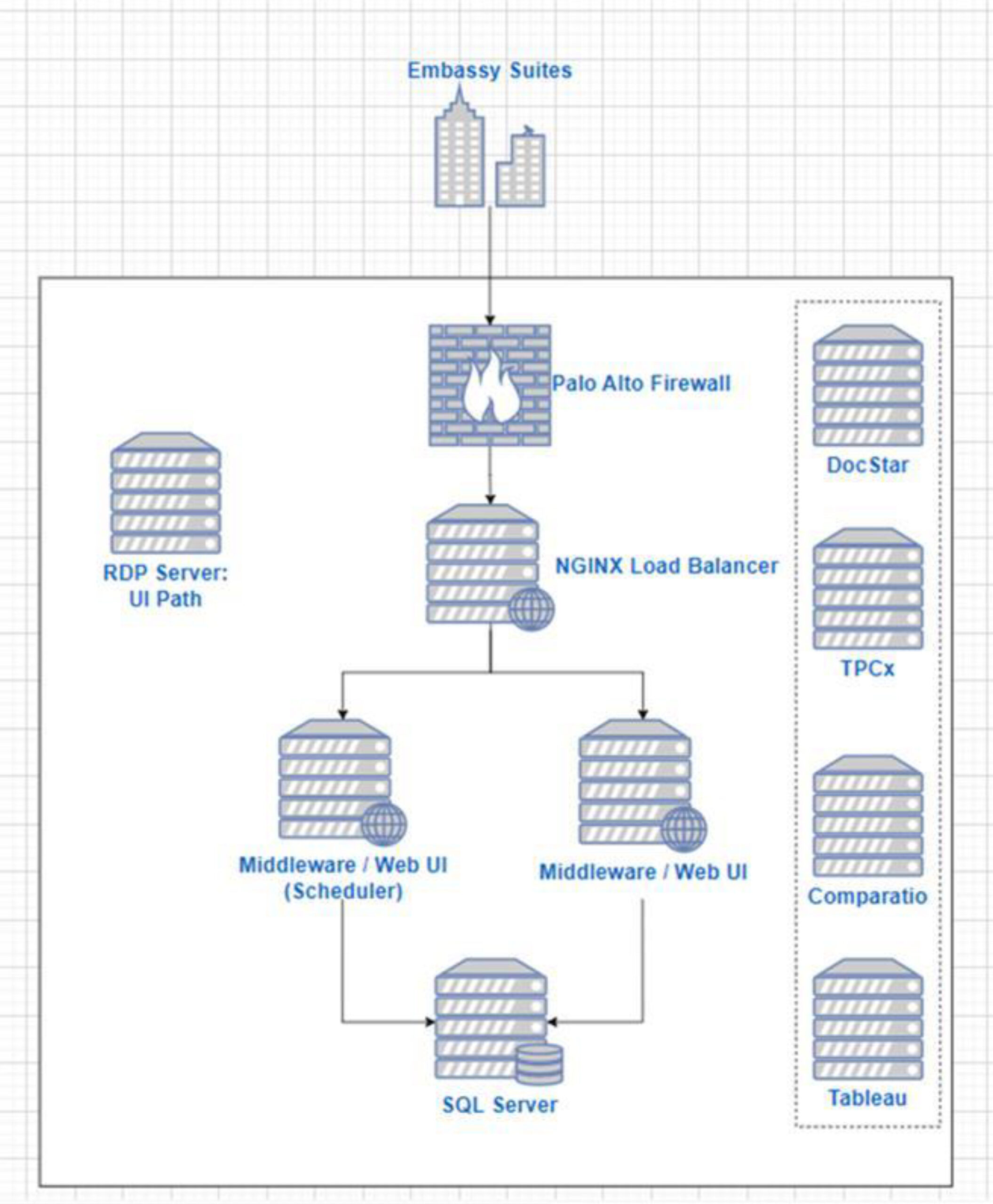
In November, EstesGroup sponsored the Southeast User Group chapter of the P21WWUG, presenting on P21 Infrastructure Best Practices and the elusive topic of Web UI Migrations. Our polls revealed that two-thirds of customers have yet to fully migrate from the P21 desktop application.
For customers still tethered to a desktop version seeking a way out, we recommend two approaches when planning a P21 Web UI migration: incremental or big bang.
An Incremental Approach
For those committed to the last branched version (2021.1) and hesitant to fully transition from the P21 desktop, an incremental approach is advisable. The customer creates an ecosystem as a live testing model, gradually shifting from the old to the new through the following steps:
- Develop an adoption plan for “branched” usage, initially allocating specific hours for web UI use.
- Configure a branched deployment in the live environment, allowing parallel use of desktop and web UI.
- Instruct users to incrementally operate on the web UI during designated hours.
- Address reported shortcomings incrementally through IT or ERP administrator intervention.
- Create a remediation work plan for identified issues and initiate resolution.
- Conduct remediation and testing cycles until all issues are resolved.
- Increase web UI usage until reaching a predefined cutoff amount of time.
- Attain user and management signoff, and officially transition all users to the web UI.
- Stabilize the live cutover environment and provide ongoing support.
A Big Bang Approach
For customers seeking a more significant leap to a web-only version (2022+), the big bang approach is recommended. This involves an implementation-level cutover executed in one decisive move:
- Deploy the Web UI to a middleware-only test environment.
- Conduct user testing, addressing and communicating issues as they arise.
- Create a remediation work plan and resolve identified issues.
- Document remediations and compile into a cutover plan, expanding the testing pool.
- Conduct a mock cutover (CRP), regression testing, and address any remaining issues.
- Attain user and management sign-off for the “go live” decision.
- Repeat the cutover to the new version in the live environment with Web UI.
- Stabilize the live cutover environment and provide ongoing support.
The Weight (and Freight) of Risk in P21 Migrations
The choice between incremental and big bang approaches depends on your risk tolerance and desired rewards. If you seek to minimize risks, choose the incremental approach. For maximizing rewards, opt for the big bang. Each approach comes with its own set of risks, rewards, and characteristics. If you need assistance with your Web UI Migration, please reach out to us!