How to Increase Cybersecurity with MDR and SOC
The Power of MDR and SOC: Enhancing Cybersecurity for Businesses
In today’s digital landscape, small and medium-sized businesses (SMBs) face a constant barrage of evolving cybersecurity threats. As cyberattacks become more sophisticated and frequent, relying solely on traditional security measures such as antivirus software, firewalls, email filtering, and basic employee training may not be sufficient to fully protect your valuable data and resources.
This is where the synergy of Managed Detection and Response (MDR) and Security Operations Center (SOC) comes into play, providing enterprise-grade security tailored for your business. Are you a manufacturer trying to adhere to rigorous compliance regulations? Are you a distributor struggling to keep up with ERP system upgrades, supply chain demands, and evolving security threats? EstesGroup maintains SOC 2 certification so that our clients enjoy peace of mind at every level.

Managed Detection and Response (MDR): Proactive Protection for Your Business
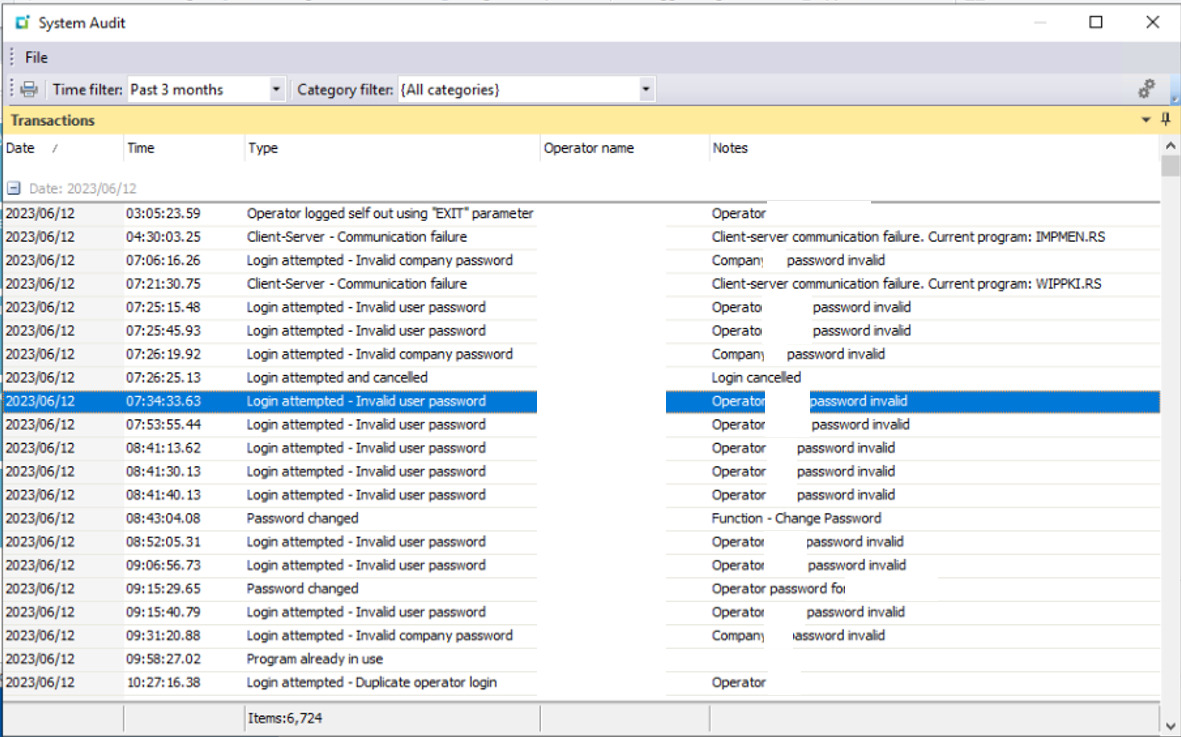
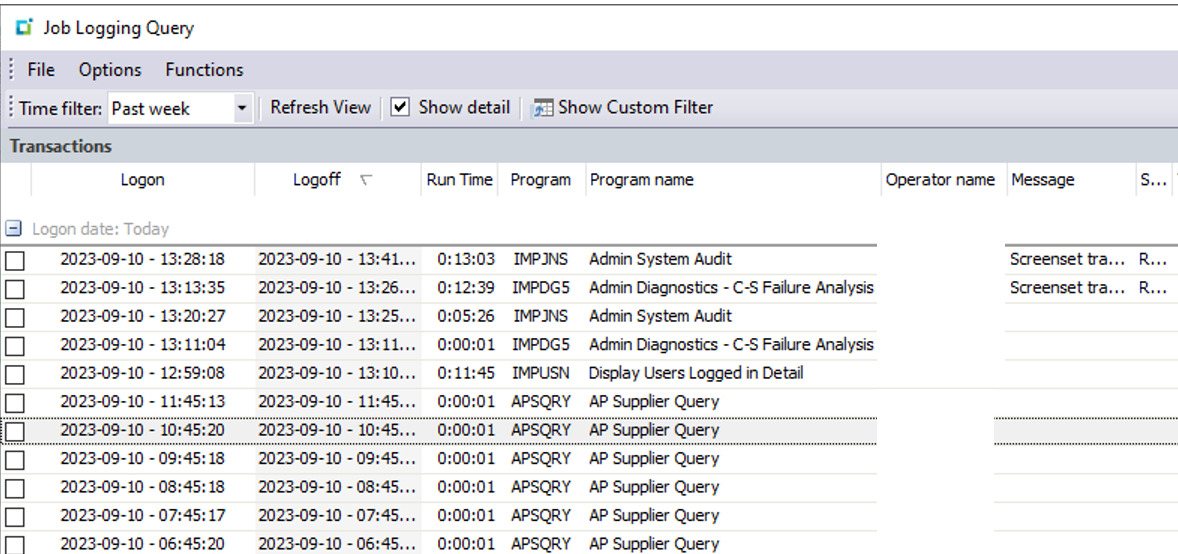
MDR is a proactive security approach that goes beyond traditional reactive measures. By leveraging advanced technologies and expert analysis, MDR provides real-time monitoring, rapid threat detection and response, instant incident alerts, and valuable insights to safeguard your data and resources. With MDR, you can rest assured that potential threats are identified and addressed promptly, minimizing the risk of a successful cyberattack.
Key Benefits of MDR
Are you looking for advanced protection? MDR employs cutting-edge technologies, such as machine learning and behavioral analytics, to detect and respond to even the most sophisticated threats. Do you need real-time monitoring? Continuous monitoring of your systems ensures that any suspicious activity is identified and addressed immediately. Are you looking for rapid response strategies? In the event of a security incident, MDR enables swift action to contain and mitigate the threat, minimizing potential damage.
Security Operations Center (SOC): 24/7 Vigilance and Expertise
Complementing MDR, a Security Operations Center (SOC) acts as a central hub for cybersecurity management. Staffed by a team of expert security analysts, the SOC provides round-the-clock monitoring, analysis, investigation, and response to potential threats.
SOC Benefits
With a secure operations center on your side, you benefit from centralized care for your entire system:
- 24/7 Monitoring: A dedicated team keeps a vigilant eye on your systems, ensuring that any suspicious activity is promptly identified and addressed.
- Expert Analysis: A skilled security analysts leverage their expertise to investigate and assess potential threats, providing valuable insights and recommendations.
- Rapid Incident Response: In the event of a security incident, your SOC team springs into action, working diligently to minimize damage and downtime, allowing you to maintain productivity.
Your Security Decisions, Your MDR and SOC
By combining MDR and SOC, you gain a comprehensive understanding of your security landscape. The insights gathered from real-time monitoring, threat analysis, and incident response empower you to make informed decisions about your cybersecurity strategy. With this knowledge, you can proactively strengthen your defenses, identify areas for improvement, and allocate resources effectively to protect your business against evolving threats.
Managed Detection and Response and a Secure Operations Center with Legacy Built on Trust
In the face of ever-evolving cyberthreats, taking proactive measures to secure your business is crucial. By embracing the power of MDR and SOC in a partnership with EstesGroup, you can enhance your cybersecurity posture and protect your business against potential attacks. Don’t wait until it’s too late – contact us today to get started on your journey towards a more secure future. We have a long-standing commitment to delivering exceptional cybersecurity solutions. With our MDR and SOC services, you can have confidence in the security of your valuable data and resources. Ask for a free demo of ECHO, EstesCloud Hosting, to learn more about managed private cloud environments for businesses. EstesGroup provides cloud solutions for companies of all sizes, across all industries, with specialized teams built for enterprise resource planning (ERP) system needs. We are the leading independent ERP consultancy for Epicor Kinetic, Epicor Prophet 21, SYSPRO, Sage, DELMIAWorks, and more!
SIGN UP FOR A CLOUD DEMO TODAY
"*" indicates required fields