5 Ways EstesGroup Helps with Your CMMC Compliance
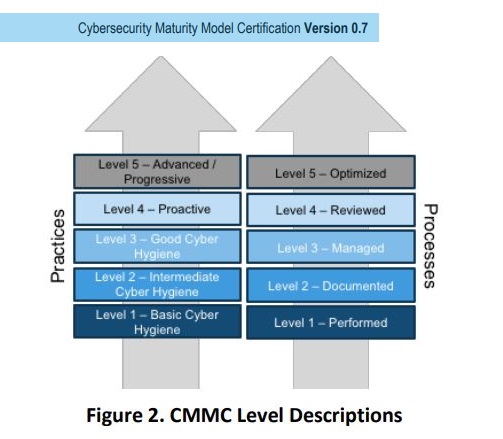
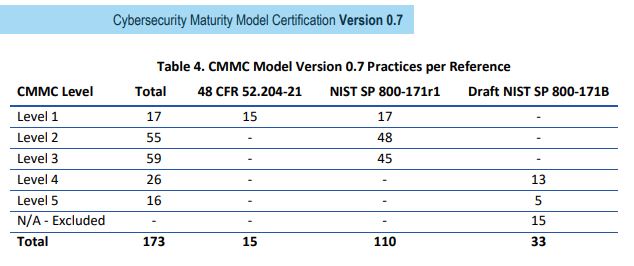
You might be reading this post if you are researching Cybersecurity Maturity Model Certification (CMMC), your company needs to become compliant, or your company is already compliant with CMMC but you have need of more IT services. In 2019 the Department of Defense announced a new cybersecurity protocol named CMMC that all DoD contractors (and some of their supply chains) would need to adhere to starting in 2020. There are 5 Levels of CMMC Certification, and EstesGroup can be an asset to companies in any of the levels.
5 Ways EstesGroup Helps with Your CMMC Compliance
- EstesGroup helps you identify the technology and/or services you need to meet your CMMC Level Requirements.
- EstesGroup can improve your Process Maturity by helping evaluate your Procedures, Policies, or Practices. Once we’ve reviewed those processes, we can help update them to ensure you meet your CMMC Level and other compliance requirements.
- There are 17 Domains that CMMC is built on. EstesGroup has the experience, tools, and services to support your business across nearly all of these domains.
- EstesGroup routinely deploys tools and managed services that directly support these CMMC domains:
- Access Control, Asset Management, Audit and Accountability, Configuration Management, Identification and Authentication, Maintenance, Recovery, Risk Management, Security Assessment, Situational Awareness, Systems and Communications Protection, and System and Information Integrity.
- EstesGroup can consult on and support technology used in these domains as well, but these domains typically require internal personnel or a third party on-site.
- Awareness and Training, Incident Response, Media Protection, Personnel Security, Physical Protection, and Risk Management
- EstesGroup routinely deploys tools and managed services that directly support these CMMC domains:
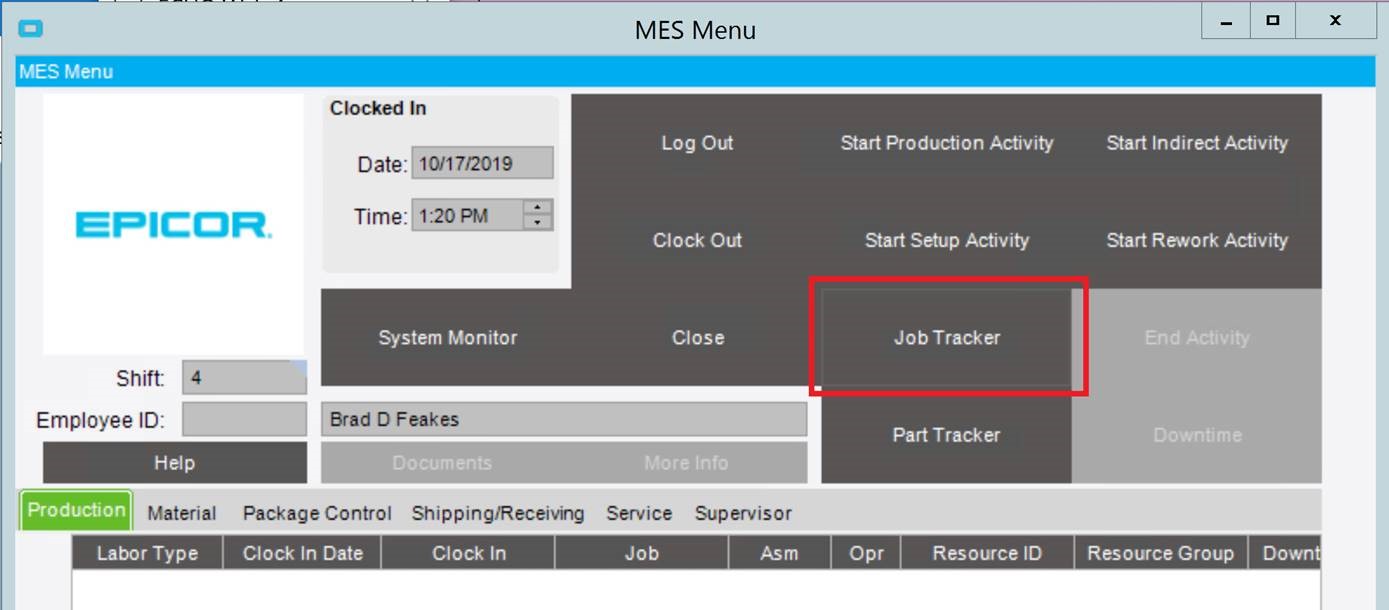
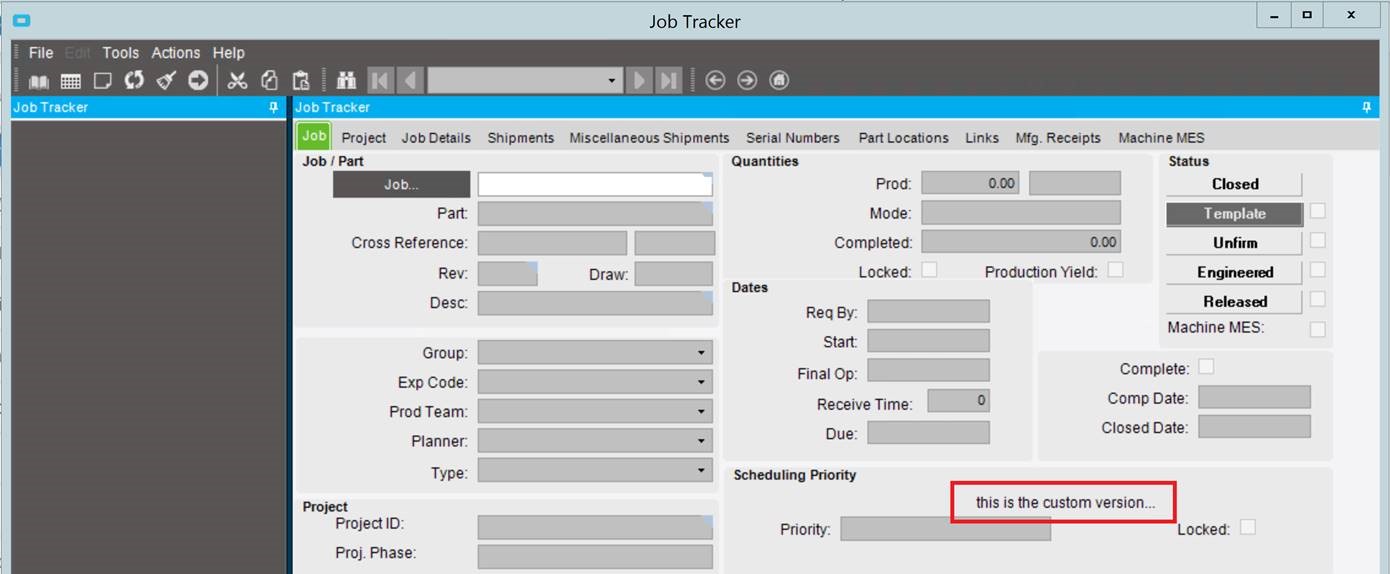
- EstesGroup Managed Services (ERP Hosting ECHO & Managed IT) employ many of the standard Cybersecurity measures required for CMMC. We regularly monitor our internal and client assets for threats, perform preventative maintenance, and update technology or processes to meet or exceed cybersecurity requirements.
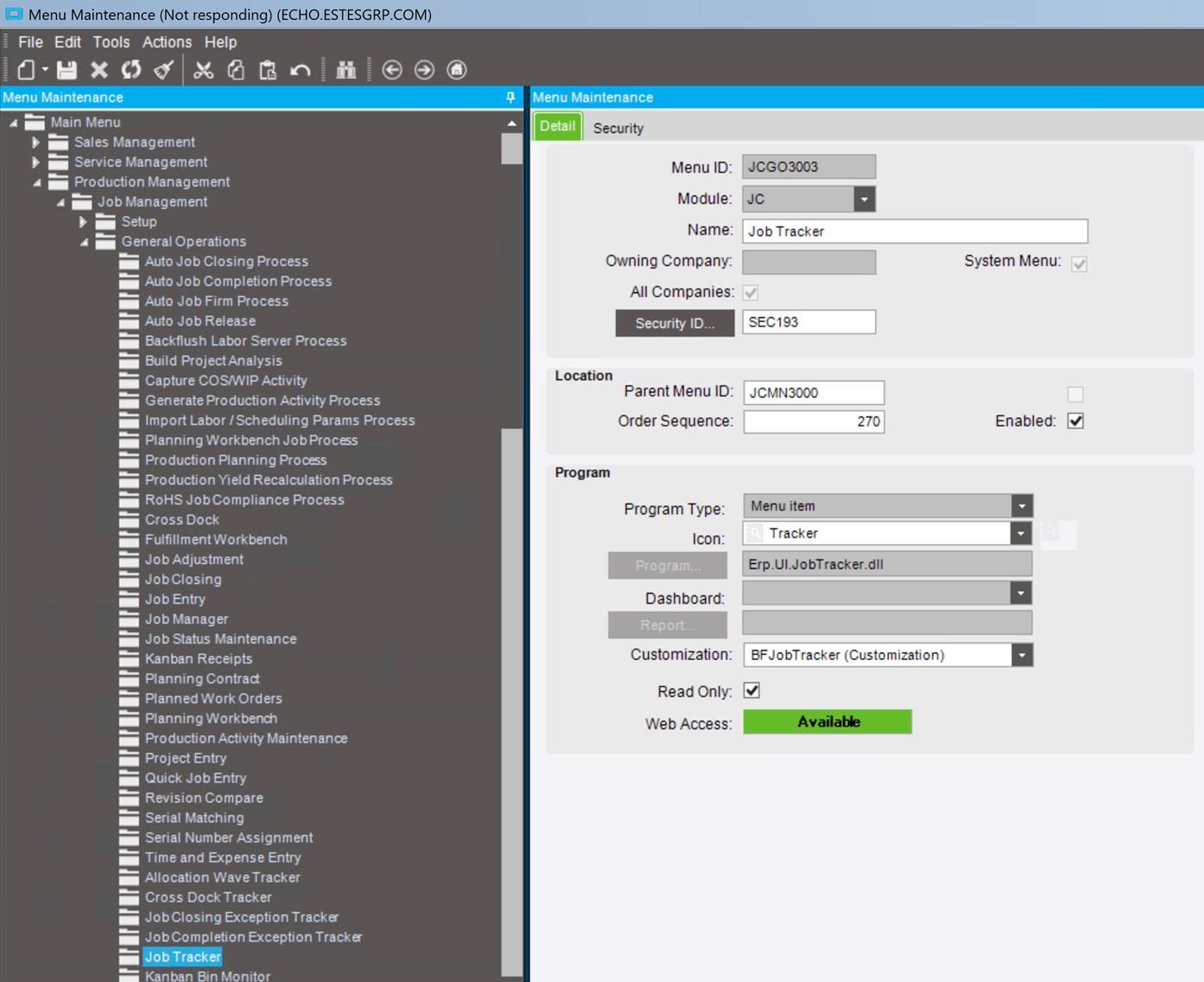
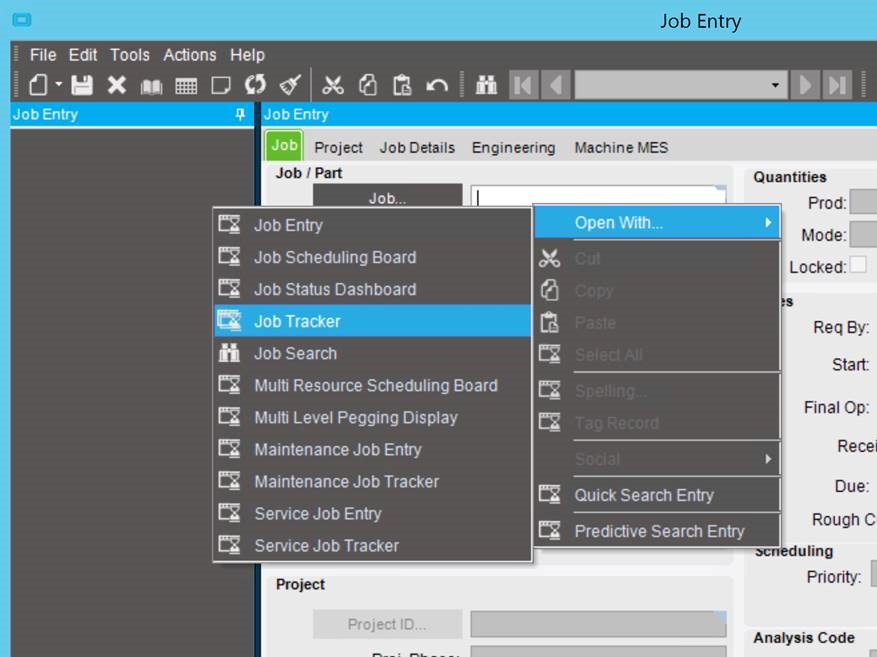
- EstesCloud Hosting (ECHO) services enable many CMMC requirements without significant impact to you, your users, or your bottom line. By hosting your servers or software solutions in a managed cloud environment, you can compartmentalize your compliant systems and protect them at the highest CMMC levels, without locking down your whole office. For more details, see our page on EstesCloud Hosting for Aerospace & Defense
To Learn about CMMC, read our blog “What is CMMC: Cybersecurity Maturity Model Certification?”
EstesGroup is a Managed Services Provider working with Manufacturing and Distribution companies by providing ERP Hosting (ECHO), Managed IT, Epicor ERP, and Prophet 21 ERP services.
Have questions about CMMC or do you want more information on how EstesGroup makes companies more secure? Contact us today!